N8n Patches Critical Remote Code Execution Vulnerability (CVE-2026-33660)
N8n is vulnerable to a critical remote code execution flaw. Tracked as CVE-2026-33660, the vulnerability has a CVSS score of 9.4. Successful exploitation of this vulnerability may allow an authenticated attacker to execute arbitrary commands on the target system.
n8n is a powerful, open-source workflow automation tool that enables users to visually design and automate complex processes by connecting various apps, APIs, and services. It functions as a digital hub, transferring data and triggering actions between tools without manual intervention, while offering deep customization through code (JavaScript/Python).
Vulnerability Details
An attacker must have the permission to create or modify workflows to exploit the vulnerability. An authenticated attacker could exploit the Merge node’s “Combine by SQL” mode to read local files on the n8n host, resulting in remote code execution. The AlaSQL sandbox did not sufficiently restrict certain SQL statements, allowing an attacker to access sensitive files on the server or even compromise the instance.
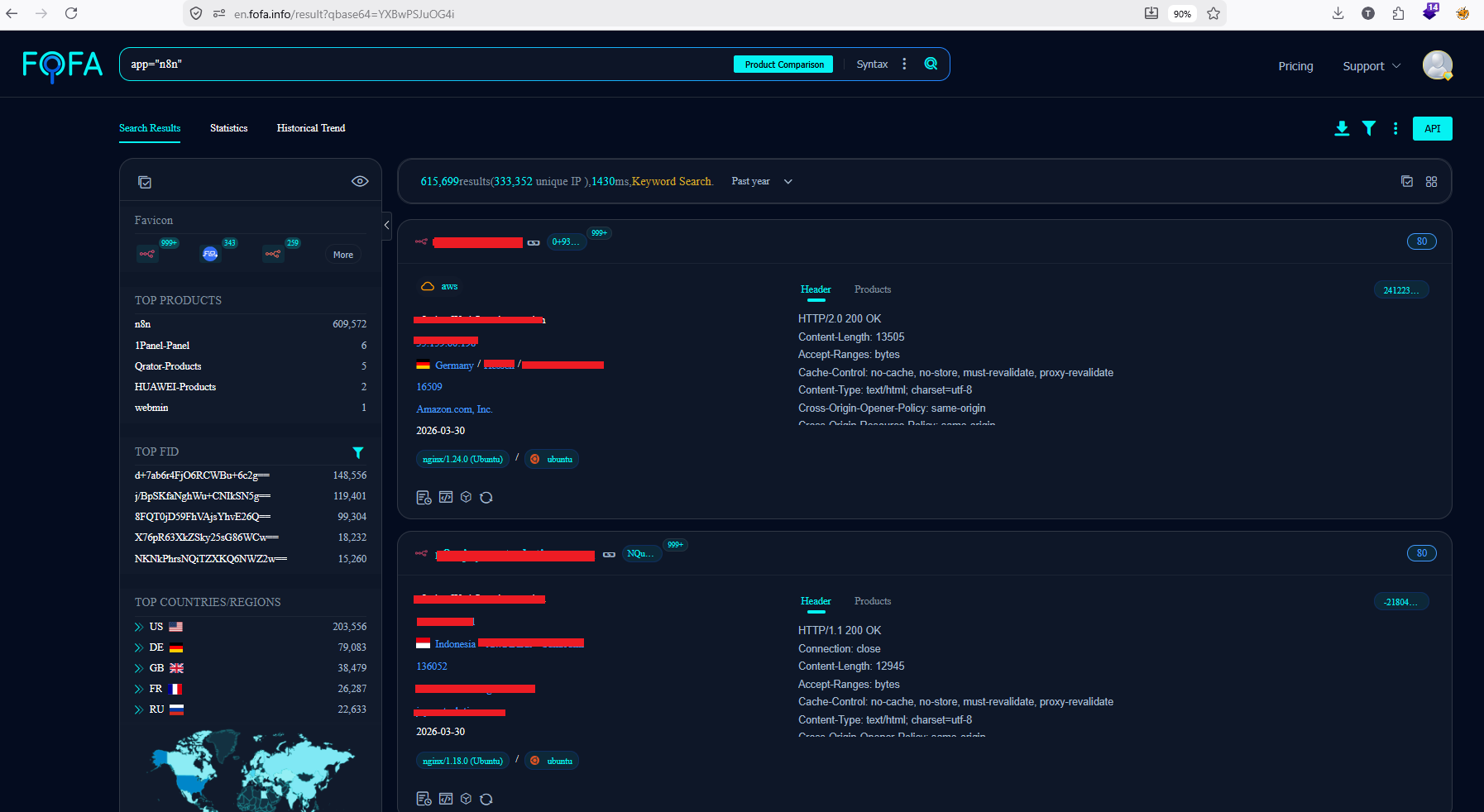
A quick search revealed more than 615,000 publicly available targets on Fofa at the time of writing.
Affected versions
The vulnerability affects the following versions:
- N8n versions before 2.14.1
- N8n versions before 2.13.3
- N8n versions before 1.123.27
Mitigation
Users must upgrade to the following N8n versions to patch the vulnerability:
- 2.14.1
- 2.13.3
- 1.123.27
For more information, please refer to the GitHub Security Advisory.
Workarounds
Administrators should consider the following temporary mitigations:
- Limit workflow creation and editing permissions to fully trusted users only.
- Disable the Merge node by adding n8n-nodes-base.merge to the NODES_EXCLUDE environment variable.
These workarounds do not fully mitigate the risk and should be used only as short-term mitigation measures.
Qualys Detection
Qualys customers can scan their devices with QID 733901 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://github.com/n8n-io/n8n/security/advisories/GHSA-58qr-rcgv-642v


Comments are closed.