Linux Kernel Vulnerability Exploited in the Wild (Copy Fail) (CVE-2026-31431)
Threat actors are exploiting a vulnerability in the Linux Kernel tracked as CVE-2026-31431. Named Copy Fail, it’s a critical Linux kernel local privilege escalation vulnerability that allows unprivileged users to gain root by corrupting the page cache of setuid binaries via the AF_ALG crypto API. The vulnerability was discovered and reported by Theori and Xint.
CISA also acknowledged the active exploitation of the vulnerability by adding it to its Known Exploited Vulnerabilities (KEV) catalog. CISA urged users to patch the vulnerability before May 15, 2026.
The Linux kernel is the open-source core component of the Linux operating system, serving as the primary interface between hardware and software processes. It acts as a bridge, managing system resources like CPU, memory, and devices (e.g., printers, disks) to ensure applications operate correctly.
Vulnerability Details
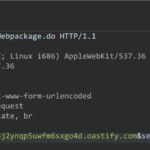
The Linux kernel vulnerability exists in the page-cache Copy-on-Write (CoW) path. The Linux kernel’s AEAD crypto implementation (algif_aead) contains a logic flaw in its handling of scatter-gather lists that allows writes beyond allocated bounds. Attackers can exploit this via AF_ALG sockets and splice() to overwrite 4 bytes in any readable file’s page cache, including setuid binaries like /usr/bin/su.
Since page cache holds in-memory copies of executables, these modifications alter binaries during Execution without changing disk files, allowing code injection into privileged programs for root access.
An attacker can exploit the vulnerability in three stages:
- Page-Cache Corruption via AF_ALG Splice Race
- Cross-Container Propagation via Image Layer Sharing
- Privileged Execution by kube-proxy
Affected versions
The vulnerability affects Linux kernel versions built between 2017 and the patch release (2026).
Linux distributors Ubuntu, RHEL, SUSE, Amazon Linux, Debian, Fedora, Arch, Rocky/Alma/Oracle Linux, having the default algif_aead module loaded, are affected by this vulnerability.
| Distribution | Current State |
| Ubuntu | Patched |
| Debian | Patched |
| RHEL | Patched |
| Fedora | Patched |
| SUSE | Patched |
| Amazon Linux | Unpatched |
| CloudLinux | Patched |
| Arch Linux | Patched |
| Upstream Linux kernel | Patched |
Mitigation
Users must upgrade to the Linux kernel versions 6.18.22, 6.19.12, and 7.0 to patch the vulnerability.
For more information, please refer to the Vendor Security Advisory.
Qualys Detection
Qualys customers can scan their devices with QID 387198 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://github.com/Percivalll/Copy-Fail-CVE-2026-31431-Kubernetes-PoC
https://git.kernel.org/pub/scm/linux/kernel/git/stable/linux.git/commit/?id=a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5


Comments are closed.