Cisco Releases Patches for SD-WAN Vulnerability Exploited in the Wild (CVE-2026-20182)
Cisco warned users about a critical vulnerability impacting the Catalyst SD-WAN Controller, tracked as CVE-2026-20182. Successful exploitation of the vulnerability may allow an attacker to bypass authentication and obtain administrative privileges on an affected system.
CISA also acknowledged the active exploitation of the CVE-2026-20182 and added it to its Known Exploited Vulnerabilities Catalog. CISA urged users to patch the vulnerability before May 17, 2026.
Cisco mentioned in their advisory that this update provides details and fixes for a vulnerability discovered and fixed after the Cisco Catalyst SD-WAN Controller Authentication Bypass Vulnerability was disclosed in February 2026.
Cisco Catalyst SD-WAN is a cloud-native, software-defined networking solution that creates a secure, automated overlay across diverse network transports (MPLS, internet, 5G) to connect branches, data centers, and clouds. It uses centralized control to manage, secure, and monitor network traffic, enabling better performance, application visibility, and lower operational costs.
CVE-2026-20182: Cisco Catalyst SD-WAN Controller Authentication Bypass Vulnerability
This vulnerability stems from an improper functioning of the peering authentication mechanism in an affected system. An attacker could exploit this vulnerability by sending crafted requests to the affected system. Successful exploitation of the vulnerability could allow an attacker to log in to an affected Cisco Catalyst SD-WAN Controller as an internal, high-privileged, non-root user account. Using this account, the attacker could access NETCONF, enabling them to manipulate network configuration for the SD-WAN fabric.
Affected and Patched Versions
This vulnerability affects all deployment types, including:
- On-Prem Deployment
- Cisco SD-WAN Cloud-Pro
- Cisco SD-WAN Cloud (Cisco Managed)
- Cisco SD-WAN for Government (FedRAMP)
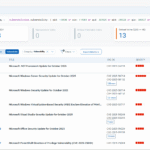
| Cisco Catalyst SD-WAN Release | First Fixed Release |
| Earlier than 20.9 | Migrate to a fixed release |
| 20.9 | 20.9.9.1 |
| 20.10 | 20.12.7.1 |
| 20.11 | 20.12.7.1 |
| 20.12 | 20.12.5.4 20.12.6.2 20.12.7.1 |
| 20.13 | 20.15.5.2 |
| 20.14 | 20.15.5.2 |
| 20.15 | 20.15.4.4 20.15.5.2 |
| 20.16 | 20.18.2.2 |
| 20.18 | 20.18.2.2 |
| 26.1 | 26.1.1.1 |
For more information, please refer to the Cisco security advisory (cisco-sa-sdwan-rpa2-v69WY2SW).
Qualys Detection
Qualys customers can scan their devices with QID 317854 to detect vulnerable assets.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.


Comments are closed.