Axios npm Supply Chain Attack: Malicious RAT Deployment
A sophisticated supply-chain attack is targeting the popular npm package Axios. Attackers compromised a lead maintainer’s account to publish malicious versions 1.14.1 and 0.30.4, injecting a hidden dependency called plain-crypto-js version 4.2.1. The dependency executes a postinstall script that acts as a cross-platform remote access trojan (RAT) dropper, targeting macOS, Windows, and Linux.
Axios is a popular, promise-based open-source JavaScript library for making HTTP requests from browsers and Node.js environments. It simplifies asynchronous communication with REST endpoints by offering features such as automatic JSON data transformation, request/response interception, and robust error handling.
These packages typically have over 100 million downloads on npm and adoption across frontend frameworks, backend services, and enterprise applications.
Google Threat Intelligence Group (GTIG) assigned this activity to UNC1069, a financially motivated North Korea-nexus threat actor active since at least 2018, based on the use of WAVESHAPER.V2, an updated version of WAVESHAPER previously used by this threat actor.
Inception of the Vulnerability
The attack began with the hijacking of the jasonsaayman npm account, whose email was altered to if****@****on.me. Attackers exploited an npm token to bypass standard GitHub release protocols. Attackers published the malicious versions without corresponding tags or OpenID Connect verification metadata.
Cross-Platform Payload Delivery
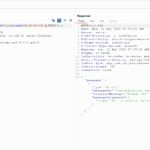
The malicious version executes a postinstall script that acts as a cross-platform remote access trojan (RAT) dropper, contacting a live command-and-control server and delivering platform-specific second-stage payloads.
The script’s sophistication shines in its OS-specific execution paths.
On macOS, it beacons to endpoints that mimic the npm infrastructure, downloading a Mach-O binary to /Library/Caches/com.apple.act.mond for persistent remote access.
Windows victims see a PowerShell dropper, staged as %PROGRAMDATA%wt.exe, which is invoked via VBScript for evasion.
Linux targets receive a Python loader at /tmp/ld.py. Each payload transmits system reconnaissance data back to the C2 and awaits commands, including peinject, which injects additional malware.
After execution, the malware deletes itself and replaces its own package.json with a clean version, leaving minimal forensic footprints beyond the plain-crypto-js folder in node_modules.
Affected Versions
The vulnerability affects Axios versions 1.14.1 and 0.30.4.
Mitigation
Users with vulnerable Axios versions installed must rotate their secrets and credentials with immediate effect and downgrade to a safe version (1.14.0 or 0.30.3). The malicious versions, as well as “plain-crypto-js,” are no longer available for download from npm.
Qualys Detection
Qualys customers can scan their devices with QIDs 386943 and 5010006 to detect vulnerable assets.
Note: QID 5010006 is available via SwCA, which needs to be enabled.
Please continue to follow Qualys Threat Protection for more coverage of the latest vulnerabilities.
References
https://socket.dev/blog/axios-npm-package-compromised



Comments are closed.